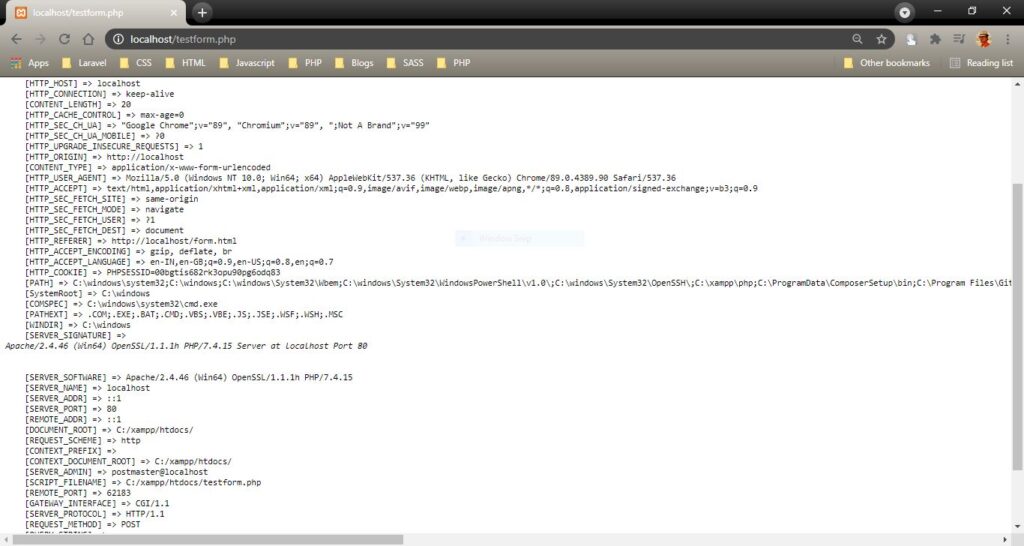
scmuser created the topic: Error validating server certificate for
I am getting error during checkout source code from Svn.
Error validating server certificate for https://XYZ:443:
– Unknown certificate issuer
Fingerprint: 81:bb:5d:da:c5:7d:fa:f3:f4:9f:06:55:c6:34:e3:b4:64:d0:47:bc
Distinguished name: www.digicert.com , DigiCert Inc, US
sgadmin replied the topic: Re:Error validating server certificate for
It seems your cache Security certification for SVN server has been expired to removed. please Click on “Accept Permanently” to get rid of this issues.
Background:
When speaking to Apache via https://, a Subversion client can receive two different types of information:
a server certificate
a demand for a client certificate
If the client receives a server certificate, it needs to verify that it trusts the certificate: is the server really who it claims to be? The OpenSSL library does this by examining the signer of the server certificate, or certifying authority (CA). If OpenSSL is unable to automatically trust the CA, or if some other problem occurs (such as an expired certificate or hostname mismatch), the Subversion commandline client will ask you whether you want to trust the server certificate anyway.
svn list host.example.com/repos/project
Error validating server certificate for ‘ home.example.com:443 ‘:
– The certificate is not issued by a trusted authority. Use the
fingerprint to validate the certificate manually!
Certificate information:
– Hostname: host.example.com
– Valid: from Jan 30 19:23:56 2004 GMT until Jan 30 19:23:56 2006 GMT
– Issuer: CA, example.com, Sometown, California, US
– Fingerprint: 7d:e1:a9:34:33:39:ba:6a:e9:a5:c4:22:98:7b:76:5c:92:a0:9c:7b
(R)eject, accept (t)emporarily or accept (p)ermanently?
This dialogue should look familiar; it’s essentially the same question you’ve probably seen coming from your web browser (which is just another HTTP client like Subversion!). If you choose the (p)ermanent option, the server certificate will be cached in your private run-time auth/ area in just the same way your username and password are cached (see the section called “Client Credentials Caching”.) If cached, Subversion will automatically remember to trust this certificate in future negotiations.
Your run-time servers file also gives you the ability to make your Subversion client automatically trust specific CAs, either globally or on a per-host basis. Simply set the ssl-authority-files variable to a semicolon-separated list of PEM-encoded CA certificates:
[global]
ssl-authority-files = /path/to/CAcert1.pem;/path/to/CAcert2.pem
Many OpenSSL installations also have a pre-defined set of “default” CAs that are nearly universally trusted. To make the Subversion client automatically trust these standard authorities, set the ssl-trust-default-ca variable to true.
When talking to Apache, a Subversion client might also receive a challenge for a client certificate. Apache is asking the client to identify itself: is the client really who it says it is? If all goes correctly, the Subversion client sends back a private certificate signed by a CA that Apache trusts. A client certificate is usually stored on disk in encrypted format, protected by a local password. When Subversion receives this challenge, it will ask you for both a path to the certificate and the password which protects it:
$ svn list host.example.com/repos/project
Authentication realm: host.example.com:443
Client certificate filename: /path/to/my/cert.p12
Passphrase for ‘/path/to/my/cert.p12’: ********
…
Notice that the client certificate is a “p12” file. To use a client certificate with Subversion, it must be in PKCS#12 format, which is a portable standard. Most web browsers are already able to import and export certificates in that format. Another option is to use the OpenSSL commandline tools to convert existing certificates into PKCS#12.
Again, the runtime servers file allows you to automate this challenge on a per-host basis. Either or both pieces of information can be described in runtime variables:
[groups]
examplehost = host.example.com
[examplehost]
ssl-client-cert-file = /path/to/my/cert.p12
ssl-client-cert-password = somepassword
Once you’ve set the ssl-client-cert-file and ssl-client-cert-password variables, the Subversion client can automatically respond to a client certificate challenge without prompting you. [24]
Tagged : server